
How concepts from the CIA Triad affect personal information
Information security and information privacy defined
While it may be easy to conflate the two, information privacy is not the same as information security. For information security professionals, the differences between the two concepts are vital. The common understanding of security is more accurately defined as confidentiality—or keeping personal information private—when in fact, the practice of information security is much broader.
Information security focuses on three concepts, known colloquially as the CIA triad:
- Confidentiality. Stored data is safe from unauthorized access.
- Integrity. Data is reliable and accurate.
- Availability. Data is available on demand.
Information privacy, on the other hand, involves:
- Collection of personal information.
- The authorized usage and disclosure of personal information.
- Data quality.
- Access to personal information.
The overlap between the concepts of information privacy and information security comes from the protection of personal information, which is a crucial concern for both. The differences between information privacy and security are illustrated below.
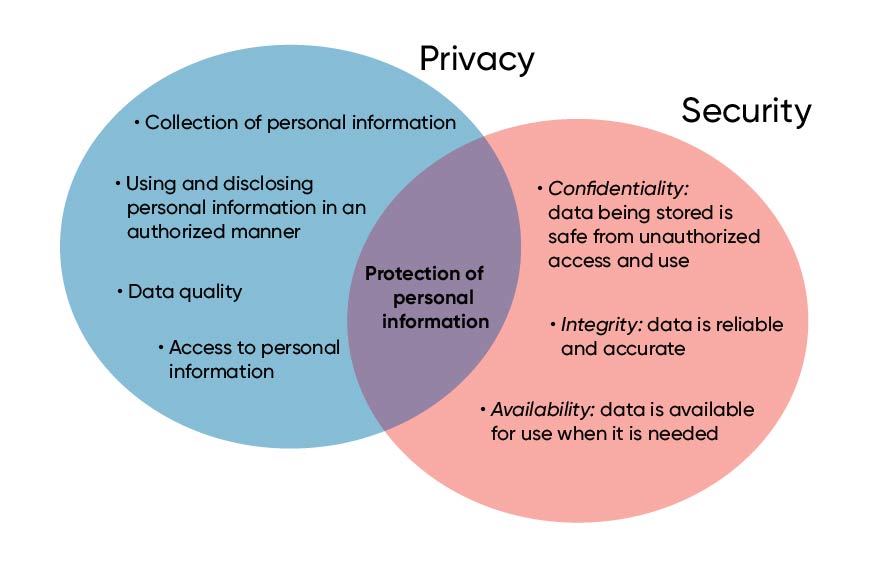
In other words:
Security is keeping the data safe, reliable, and available on demand.
Privacy is how personal data is used and controlled. Privacy focuses on how companies collect, use, and ensure the accuracy of personal information.
Learn more: What to look for in a cloud security partner
Examples of information security and information privacy
Amazon
Privacy
When shopping on Amazon, the expectation is that your information will remain confidential. Examples of personal data include mailing and billing addresses, payment information, items purchased, items searched for, and the frequency of purchasing. (Note that none of this information is personally identifiable information (PII) except payment details. Simply put, PII is any information that can verify the identity of a user, such as social security number, birth date, etc.)
Ultimately, Amazon stores data about you that you would most likely want to keep private. Any shopper shares these details with simple expectations. The retailer should:
- Keep that information safe.
- Not disclose that information to outside parties.
- Restrict access to your data to authorized personnel.
The fact that these privacy expectations are largely false—Amazon does sell this information to marketers for a tremendous profit—is a separate topic. However, it is a compelling reason to thoroughly read the privacy policy of each vendor you do business with online. Read Amazon’s privacy policy here.
Security
Even though Amazon may not live up to privacy expectations, it must make security a primary concern to stay competitive in its industry. Hence, the CIA triad.
Amazon ensures the information they are storing about you is kept confidential. In this case, confidentiality means they keep the personal information about customers out of the hands of cyber criminals and competitors.
Amazon maintains data integrity by ensuring it can’t be altered by mistake or by unauthorized users. For example, they make sure an order for a single pair of socks is not changed to ten pairs. Amazon also wants to make sure data is available. Users can view their orders anytime, day or night, from anywhere on any device. It also wants to ensure the information is available on demand for fulfillment centers to facilitate packaging the right quantities, shipping to the correct address, charging the right credit card, and so forth.
FakeBank
Privacy
In contrast to Amazon, the information banks store is PII. More examples of PII include your full name, address, age, social security number, the balance of credit and debit cards, mortgage balances, savings and checking account details, payroll amount, and the frequency of your pay. Both consumers and FakeBank want to keep personal information private.
Federal regulations demand that PII and personal credit card information (PCI) are kept confidential. Additionally, FakeBank wants you to feel like you can trust them with this very private information. Banks also sell a limited amount of personal information (non-PII and non-PCI) based on the privacy agreements signed when opening an account. FakeBank does not have a privacy agreement, but to learn more about bank privacy agreements, check out Bank of Canada’s Protection of Personal Information Policy.
Security
Banks also follow the CIA triad to keep personal information secure. FakeBank is responsible for keeping personal information confidential. Only authorized users can view social security numbers, savings and checking balances, etc.
FakeBank must also guarantee the integrity of PII and PCI. It must ensure that account balances are not manipulated in any way.
Finally, FakeBank also wants to ensure account information data is always available. Customers need to be able to check the balance of checking or savings accounts as needed. Additionally, FakeBank must confirm that your account’s balance is correct and money is accessible at any time.
In this case, the bank needs to keep customer information confidential and available and maintain the integrity of your data so that it is used appropriately per the privacy terms you agreed to when you opened the account.
Also read: I just met a vuln named Follina
Learning from the information privacy and information security experts
As we’ve seen, the differences between privacy and security can change how companies handle sensitive data. Some companies provide options for limiting how your personal information is shared with other companies. Those details are in the company’s privacy policies, which can typically be found online. If you want to limit what Amazon or your bank knows about you, review the data-sharing policies for the companies you use.
Managing information privacy and security are thorny issues for both consumers and companies. It can be complex because of changing compliance regulations and ever-evolving technology. The experts at OnX are deeply experienced in security. Additionally, they provide managed services in advanced cloud security and networking. Our consultants are passionate about helping you protect your business through education and high-quality solutions. Get in touch today, and take the first step toward implementing best-in-class security and privacy practices.
















